A case study on Taashee'smigration of a pharma sectorclient from Google CloudPlatform to Microsoft Azure,encompassing a comprehensiveoverhaul of networking,storage, database...
Learn MoreThe client approached us to create a complete DevSecOps pipeline for their existing infrastructure, which would include continuous integration (CI), continuous delivery and deployment (CD), continuous testing, continuous logging and monitoring, auditing and governance, and operations. Our DevSecOps experts created an architecture on AWS that covered the aforementioned practices, including SCA (Software Composite Analysis), SAST (Static Application Security Testing), DAST (Dynamic Application Security Testing), and an aggregation of vulnerability findings.
Our client is an established healthcare services provider headquartered in India, with global footprints in South Asia and the Middle East. Besides maintaining a massive hospital chain infrastructure across multiple cities, our client has also ventured heavily into related verticals like pharmacies, diagnostic centers, home care and online doctor consultations.
The client required an end-to-end DevSecOps solution for their existing infrastructure with a few special features. The DevSecOps pipeline had to include CI/CD, continuous testing, continuous logging and monitoring, auditing and governance, and operations. It had to be integrated with various open-source scanning tools, such as SonarQube, PHPStan, and OWASP Zap for SAST and DAST analysis. The vulnerability findings had to be aggregated in the Security Hub as a single pane of glass. The security of the pipeline had to be implemented using AWS cloud native services and the DevSecOps pipeline was to be provided as code using AWS CloudFormation.
Taashee’s DevSecOps experts first appraised the client’s unique requirements and created a solution from scratch using AWS services and other open-source tools as described below.
Services and tools
In this section, we discuss the various AWS services and third-party tools used in this solution.
CI/CD services
For CI/CD, we use the following AWS services:
Continuous testing tools
The following are open-source scanning tools that were integrated into the pipeline to meet the client’s specific requirements.
Pipeline Architecture
The following diagram shows the architecture of the solution.
Auditing and governance services
The following AWS auditing and governance services were used for this implementation:
Operations services
The following AWS auditing and governance services were used for this implementation:
Continuous logging and monitoring services
The following AWS services were used for continuous logging and monitoring:

Fig. AWS DevSecOps CICD pipeline architecture
The main workflow was as follows
Security of the pipeline is implemented by using IAM roles and S3 bucket policies to restrict access to pipeline resources. Pipeline data at rest and in transit is protected using encryption and SSL secure transport. We used Parameter Store to store sensitive information such as API tokens and passwords.
Security in the pipeline is implemented by performing the SCA, SAST and DAST security checks.
As a best practice, encryption was enabled for the code and artefacts, whether at rest or transit.
Deploying the pipeline
To deploy the pipeline, we implemented the following steps:
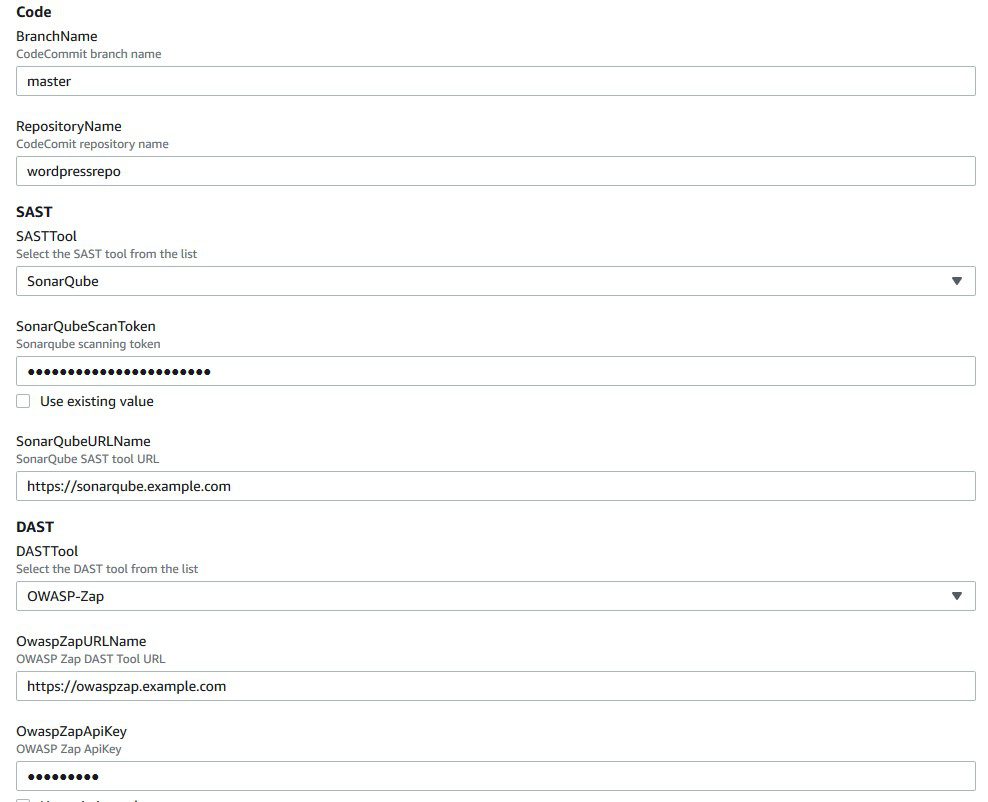
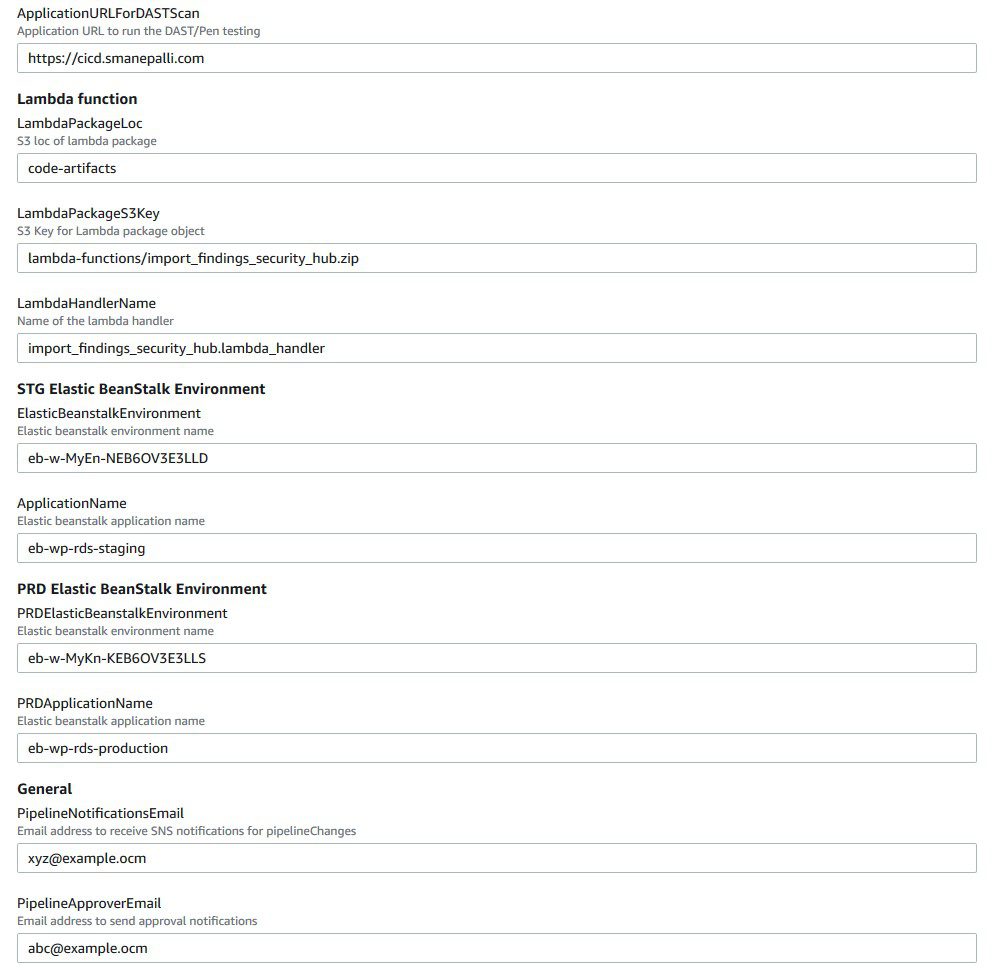
Fig. CloudFormation template deployment
Note: The provided CloudFormation template in this solution was formatted for AWS GovCloud
Running the pipeline
To trigger the pipeline, one has to commit changes to the application repository files. That generates a CloudWatch event and triggers the pipeline. CodeBuild scans the code and if there are any vulnerabilities, it invokes the Lambda function to parse and posts the results to Security Hub.
When posting the vulnerability finding information to Security Hub, we need to provide a vulnerability severity level. Based on the provided severity value, Security Hub assigns the label as follows. The client could adjust the severity levels in the code based on their requirements.
The following screenshot shows the progression of the pipeline
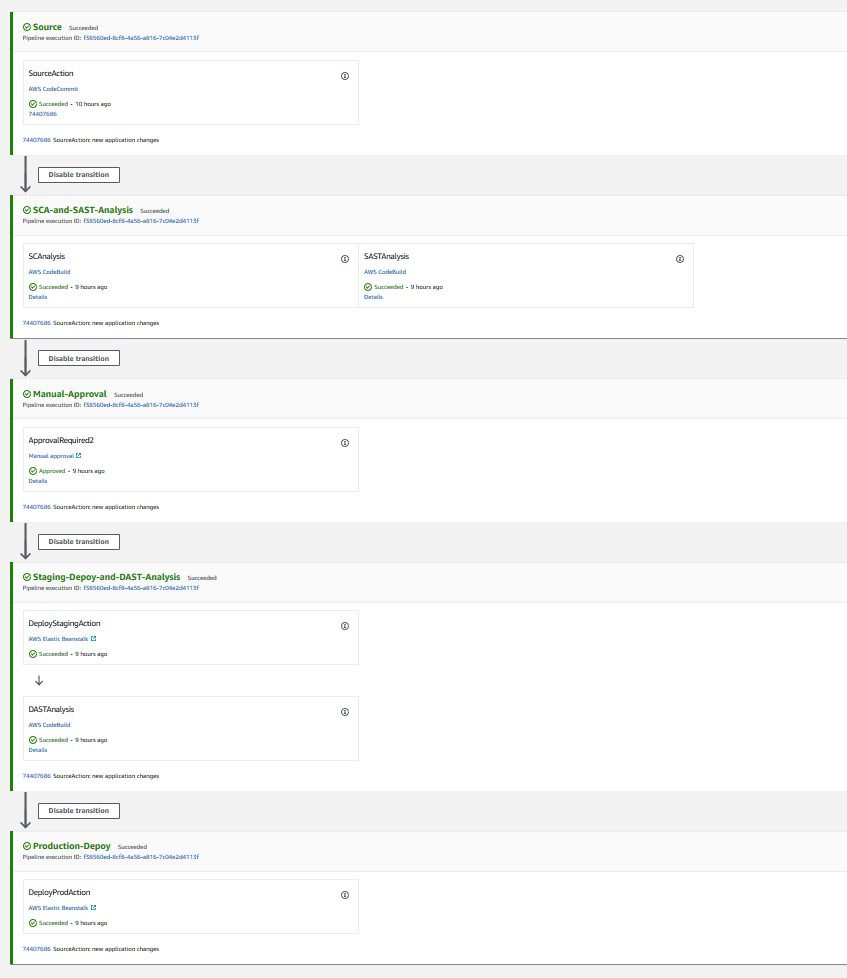
Fig. CodePipeline stages
SCA and SAST scanning
In our architecture, CodeBuild triggers the SCA and SAST scanning in parallel.
Scanning with OWASP Dependency-Check (SCA)
The following is the code snippet from the Lambda function, where the SCA analysis results are parsed and posted to Security Hub. Based on the results, the equivalent Security Hub severity level (normalized_severity) is assigned
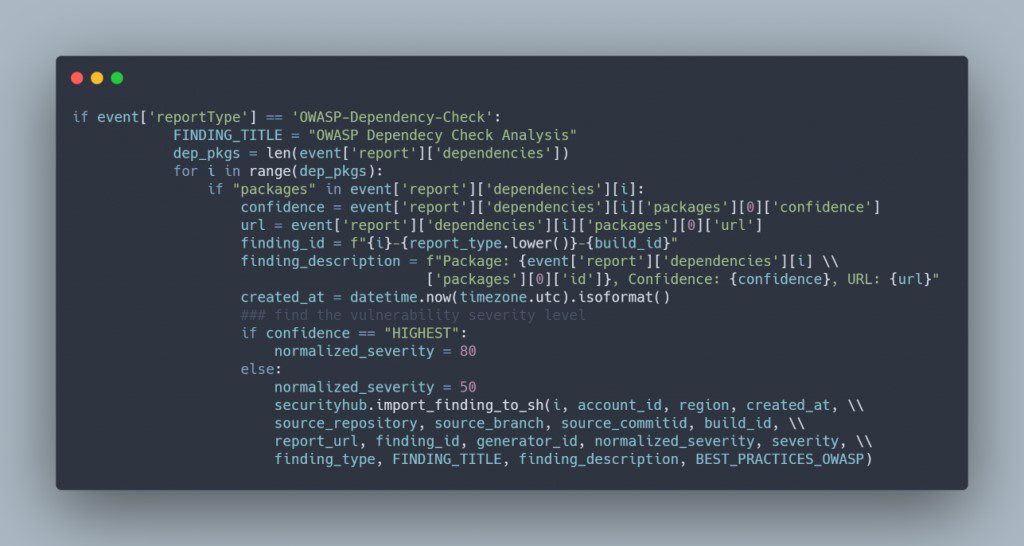
Fig. Lambda code snippet for OWASP Dependency-check
The results can be seen in the Security Hub, as in the following screenshot.

Fig. SecurityHub report from OWASP Dependency-check scanning
Scanning with SonarQube (SAST)
The following is the code snippet from the Lambda function, where the SonarQube code analysis results are parsed and posted to Security Hub. Based on SonarQube results, the equivalent Security Hub severity level (normalized_severity) is assigned.

Fig. Lambda code snippet for SonarQube
The following screenshot shows the results in Security Hub.
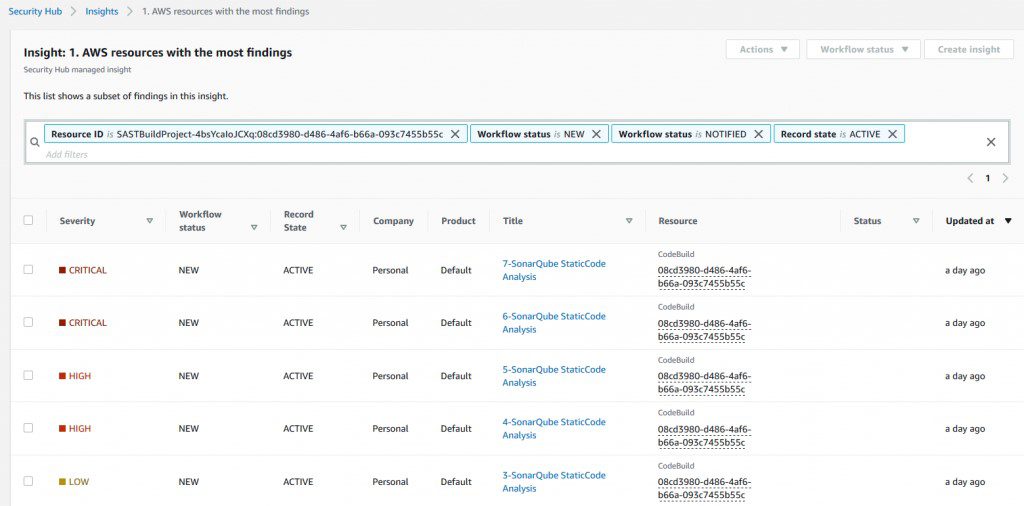
Fig. SecurityHub report from SonarQube scanning
Scanning with PHPStan (SAST)
The following is the code snippet from the Lambda function, where the PHPStan code analysis results are parsed and posted to Security Hub.
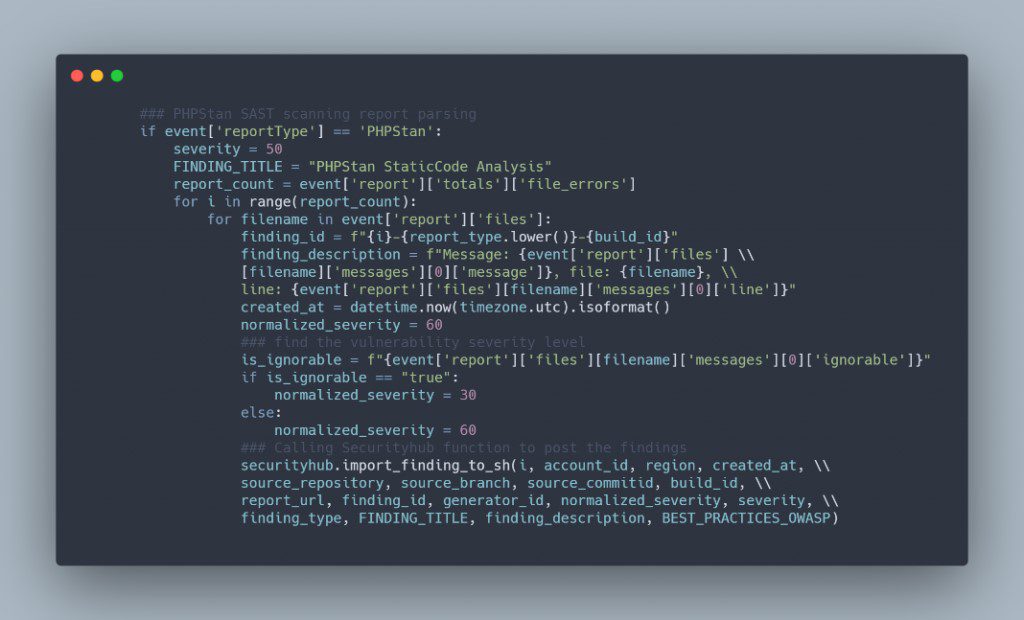
Fig. Lambda code snippet for PHPStan
The following screenshot shows the results in Security Hub.
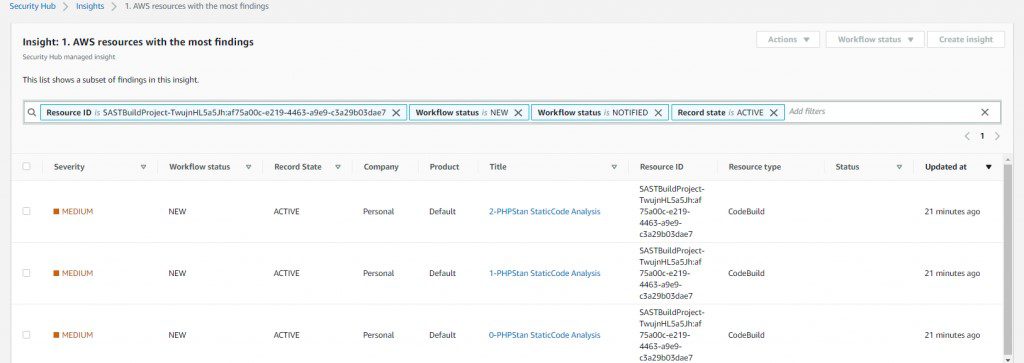
Fig. SecurityHub report from PHPStan scanning
DAST scanning
In our architecture, CodeBuild triggers DAST scanning and the DAST tool.
If there are no vulnerabilities in the SAST scan, the pipeline proceeds to the manual approval stage and an email is sent to the approver. The approver can review and approve or reject the deployment. If approved, the pipeline moves to next stage and deploys the application to the provided Elastic Beanstalk environment.
Scanning with OWASP Zap
After deployment is successful, CodeBuild initiates the DAST scanning. When scanning is complete, if there are any vulnerabilities, it invokes the Lambda function similar to the SAST analysis. The function parses and posts the results to Security Hub. The following is the code snippet of the Lambda function.
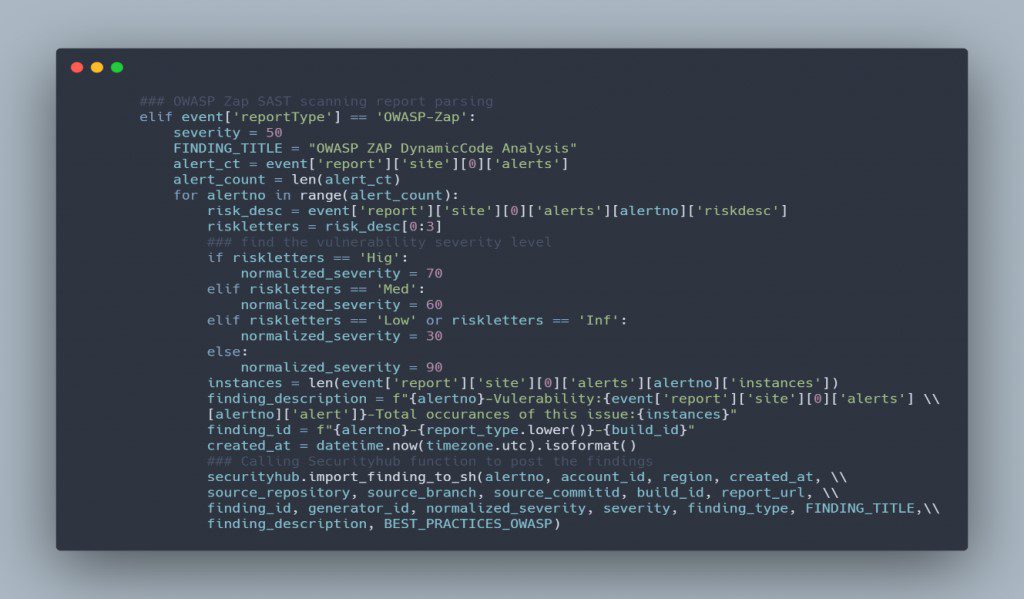
Fig. Lambda code snippet for OWASP-Zap
The following screenshot shows the results in Security Hub

Fig. SecurityHub report from OWASP-Zap scanning
Aggregation of vulnerability findings in Security Hub provided opportunities to automate the remediation. For example, based on the vulnerability finding, the client could trigger a Lambda function to take the needed remediation action. This also reduced the burden on operations and security teams because they could now address the vulnerabilities from a single pane of glass instead of logging into multiple tool dashboards.
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
This is the heading
Taashee’s technical team helps organizations that require increased developer productivity, higher quality applications, and lower maintenance costs. Taashee programmers specialize in multiple technologies with add-on features and advanced support. The biggest advantage for customers approaching Taashee is that they do not need to approach multiple vendors to implement different technologies.
A case study on Taashee'smigration of a pharma sectorclient from Google CloudPlatform to Microsoft Azure,encompassing a comprehensiveoverhaul of networking,storage, database...
Learn MoreA case study on how Taasheeachieved a scalable messagingsystem for implementing IBMSecurePay in a hybrid cloudenvironment
Learn MoreTaashee assisted an Insurance IT firm in migrating to a customized HIPAA-compliant AWS infrastructure using cost-effective tools and AWS native...
Learn MoreMon – Fri: 9.30 am – 6.30 pm
Sat – Sun: Closed
Taashee Linux Services Private Limited is a leading open-source technology company with a global footprint specializing in technology integration, application transformation, custom IT solutions that are woven intricately around path-breaking concepts.
© 2007-2023 Taashee Linux Services Private Limited – All Rights Reserved